Default passwords are the quickest way to compromise your network because they are widely known or easy to guess. Cybercriminals often exploit these by using automated tools to crack simple or factory-set passwords within seconds. If you don’t change default credentials, you leave your devices open to attack. Protect your network by updating passwords and following best security practices. Keep going, as you’ll uncover more ways to keep your systems safe.
Key Takeaways
- Default passwords are widely known or easily guessable, enabling quick unauthorized access if not changed.
- Attackers use brute force methods to rapidly crack default credentials and compromise networks.
- Many devices remain vulnerable due to unchanged default passwords, facilitating quick exploitation.
- Weak default passwords undermine brute force protections, increasing the risk of network breaches.
- Changing default passwords and implementing strong security practices are essential to prevent network compromises.
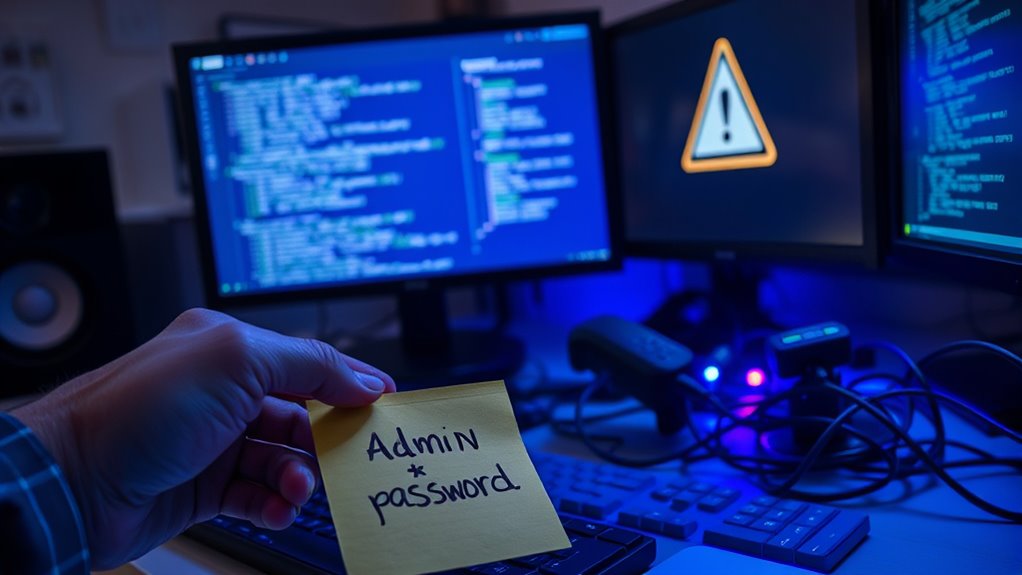
Have you ever wondered why so many devices and accounts are vulnerable right out of the box? The answer often lies in the default passwords manufacturers set. These default credentials are widely known or easily guessable, making them a prime target for cybercriminals. Attackers often use brute force methods—systematic guessing of passwords—to gain unauthorized access. Without proper safeguards, these automated attacks can crack weak default passwords in seconds. That’s why brute force prevention measures are vital; they help block repeated login attempts and slow down or stop attackers before they succeed. Many systems include account lockouts after a certain number of failed attempts, but these aren’t foolproof if the default passwords are weak or unchanged.
One of the biggest issues with default passwords is their lack of password complexity. Manufacturers often use simple, common, or generic passwords because they’re easy to remember and set up. However, this simplicity becomes a significant vulnerability once someone tries to access the device or account maliciously. If you leave the default password unchanged, you’re basically inviting hackers to exploit that weakness. Password complexity involves creating passwords that are long, unique, and include a mix of letters, numbers, and special characters. By increasing password complexity, you make it exponentially harder for brute force attacks to succeed, especially if combined with other security measures like account lockouts or rate limiting. Additionally, using proper password management practices can help ensure passwords are both strong and unique across all your accounts.
The problem gets worse if you ignore changing default passwords altogether. Many users neglect this step because they’re unaware of the risks or find it inconvenient. Cybercriminals, however, are well-aware of common default credentials and often scan networks for devices still using factory settings. Once they identify these, they can quickly gain access, often without much effort. That’s why changing default passwords should be the first step in securing any device or account. Creating a complex password isn’t just about adding length; it’s about making it unpredictable. Avoid common passwords, predictable sequences, or simple patterns. Instead, aim for a password that combines random characters, words, and symbols, making brute force attacks impractical.

TP-Link AX1800 WiFi 6 Router (Archer AX21 V5) – Dual Band Wireless Internet, Gigabit, Easy Mesh, Works with Alexa – A Certified for Humans Device, Free Expert Support
DUAL-BAND WIFI 6 ROUTER: Wi-Fi 6(802.11ax) technology achieves faster speeds, greater capacity and reduced network congestion compared to…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Often Do Hackers Exploit Default Passwords in Real-World Attacks?
Hackers frequently exploit default passwords in real-world attacks, especially when you reuse simple passwords or neglect password complexity. They scan networks for devices with default credentials, knowing many users don’t change them. If you stick to weak, reused passwords, you’re more vulnerable. Regularly updating passwords, avoiding default ones, and using complex combinations considerably reduce your risk, making it harder for hackers to gain access through these common vulnerabilities.
Are There Industries More Vulnerable to Default Password Breaches?
You should know that over 70% of IoT vulnerabilities stem from default passwords, making healthcare industries particularly vulnerable to breaches. These sectors often overlook securing devices, risking sensitive patient data and critical systems. If you ignore default password risks, hackers can easily exploit weak security, leading to severe healthcare risks and compromised networks. It’s essential to change default passwords immediately to protect your systems and sensitive information.
What Tools Do Hackers Use to Discover Default Passwords?
Hackers use tools like password guessing and brute force techniques to discover default passwords. They rely on automated software, such as Hydra or Medusa, to systematically try common or predictable passwords until they succeed. These tools speed up the process, making it easier to break into networks that haven’t changed default credentials. You should always update default passwords to prevent hackers from exploiting this common vulnerability.
How Can Businesses Automate Default Password Management Securely?
Think of your network as a fortress; you wouldn’t leave the gates unguarded. To automate default password management securely, you set up robust password policies and implement credential rotation. Use trusted password management tools that automatically generate, store, and update passwords without human error. This way, your defenses stay sharp, and default passwords become a thing of the past, keeping your network safe from unwelcome intruders.
What Are the Legal Implications of Using Default Passwords?
Using default passwords can lead to legal issues if you don’t follow cybersecurity regulations and enforce strict password policies. You might face penalties or lawsuits if a breach occurs due to negligence. It’s essential that you implement strong password management practices, regularly update passwords, and adhere to relevant laws to protect your business and avoid legal liabilities. Ensuring compliance demonstrates your commitment to cybersecurity and minimizes potential legal risks.
Password Manager: My Personal Organizer for Passwords and PINs: Manage and Securely Access All Your Passwords Offline
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
Leaving default passwords unchanged is like locking your front door but leaving a spare key under the mat. It might seem simple, but it makes your network an easy target for hackers. While setting up your devices quickly feels convenient, neglecting this step exposes your data to risks you can’t see. Don’t let complacency be your weakest link. Take a moment now—change those defaults—and turn your network into a fortress, not an open invitation.

RecZone LLC Password Safe Electronic Storage Organizer Keeper Device and Stylus Bundle
Securely Remember All Your Passwords, Log-in's, User Names, ATM PIN Numbers and More
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Door Knob Lock Combination Child Proof Door Knob Cover Lock Out Device for Bedroom, Bathroom, Faucet, Water Gas Valve, Temporary Door Handle Lock Prevents Access to Keyhole Dementia Elderly
UPGRADE PASSWORD DUAL PROTECTION: This door knob lockout device is designed with code lock. No need to carry…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.