Security questions are a major security problem because their answers often rely on personal details that attackers can easily find through social engineering, data breaches, or online searches. Since many people reuse answers across platforms, a breach on one site can expose your accounts everywhere. Automated tools can quickly guess or retrieve your answers, making your accounts vulnerable. To understand how this weak link risks your security and what you can do about it, keep exploring further.
Key Takeaways
- Security questions often rely on easily discoverable personal information vulnerable to social engineering and phishing attacks.
- Data breaches expose answers to security questions, making them accessible to cybercriminals on the dark web.
- Static security questions do not adapt to evolving threats and become obsolete as personal data leaks increase.
- Automated tools can quickly test common answers using publicly available information, increasing the risk of unauthorized access.
- Modern verification methods like biometrics offer stronger, dynamic security, rendering traditional security questions obsolete.
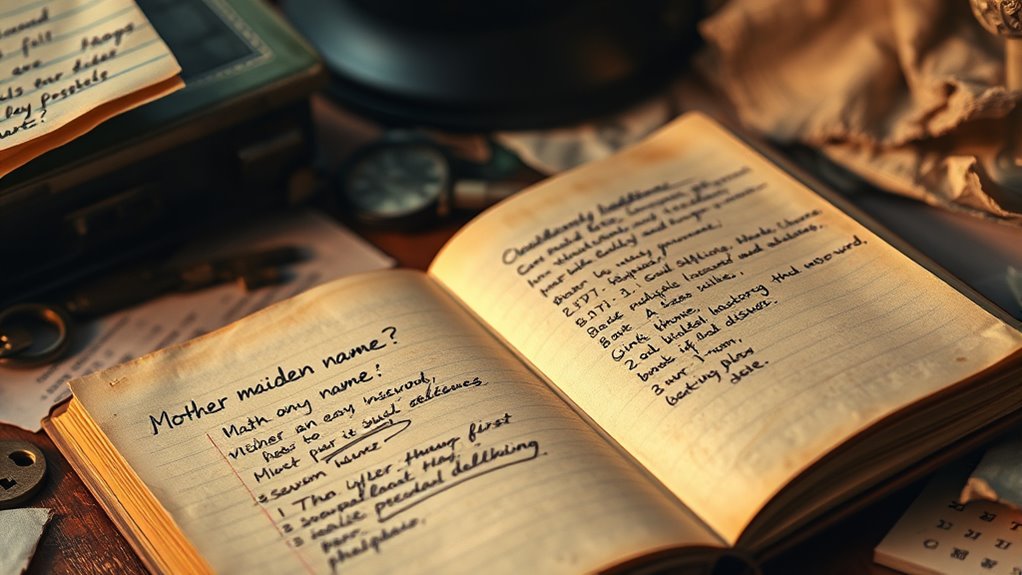
Security questions, once a common way to verify your identity, have become a significant security risk. These questions often rely on personal information that’s easy for attackers to discover or guess. As a result, they’re increasingly targeted by cybercriminals using social engineering tactics. Social engineering involves manipulating or deceiving you into revealing sensitive details, often through seemingly harmless interactions. Attackers might call customer service pretending to be you, or craft convincing phishing emails that prompt you to disclose your favorite pet’s name or the name of your first school. Once they obtain this information, they can bypass security questions and gain access to your accounts. This makes security questions a weak link in your overall security, especially since many people reuse the same answers across multiple platforms. If one account gets compromised, hackers can leverage that information to access others, compounding the damage. Additionally, ear wax odor can sometimes be an indicator of underlying health issues, which, if exploited, could lead to further privacy concerns. Data breaches also play a significant role in undermining the effectiveness of security questions. Major breaches expose vast amounts of personal data, including the answers you’ve set for security questions. When your data is leaked online, malicious actors can easily search for this information on the dark web or hacking forums. They don’t need to guess anymore; they just look up what’s already out there. This widespread availability turns what was supposed to be a personalized security measure into an open book for cybercriminals. Even if you choose obscure answers, data breaches can make your entire security setup vulnerable. Once your personal details are publicly accessible, attackers can use automated tools to test common security questions and find matches, allowing them to break into your accounts effortlessly. Furthermore, security questions don’t adapt well to modern cybersecurity threats. They’re static, meaning once your answers are known or guessed, they’re useless. Unlike two-factor authentication or biometric verification, security questions don’t provide additional layers of protection. They’ve become an antiquated method that offers a false sense of security rather than real protection. This misconception can lead you to believe your account is safer than it actually is, making you less cautious. In today’s digital landscape, hackers leverage social engineering and data breaches to exploit these vulnerabilities, making security questions more of a liability than an asset. It’s time to move to more secure verification methods that keep your personal information protected and reduce your risk of falling victim to cyberattacks.

aosu Security Cameras Outdoor Wireless, 4 Cam-Kit, No Subscription Required, Solar-Powered, Home Security Cameras System with 360° Pan & Tilt, Auto Tracking, 2K Color Night Vision, Easy Setup
No Subscription Required with aosuBase: All recordings will be encrypted and stored in aosuBase without subscription or hidden...
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Do Hackers Typically Exploit Security Questions?
Hackers often exploit security questions by using personal data they find online or through social engineering techniques. They research your social media profiles, gather clues about your childhood pet or mother’s maiden name, and then answer security questions easily. By manipulating or tricking you into revealing personal data, they bypass security measures, gaining unauthorized access to your accounts. Always be cautious about sharing personal information publicly to protect yourself.
Are There Better Alternatives to Security Questions?
Yes, there are better alternatives for password reset and identity verification. You can use multi-factor authentication, which combines something you know, like a password, with something you have, like a mobile device, or biometric verification, such as fingerprint or facial recognition. These methods are more secure because they’re harder for hackers to bypass. By adopting these, you considerably reduce the risk of unauthorized access during password resets and identity verification processes.
How Can I Create More Secure Security Questions?
To create more secure security questions, focus on personalized security measures that reduce vulnerabilities. Avoid common questions with predictable answers, like pet names or birthdays. Instead, choose questions that only you can answer, such as unique memories or specific details. Be creative and specific, making it harder for attackers to guess. This minimizes security question vulnerabilities and strengthens your overall account protection.
Do Security Questions Comply With Data Privacy Laws?
A stitch in time saves nine, and when it comes to privacy concerns, security questions often fall short. They may not fully comply with data privacy laws because they rely on personal info that could be exposed or misused. You need to guarantee that your security questions meet legal standards for privacy and data handling, or you risk compromising your account’s security and facing legal consequences.
What Are the Best Practices for Managing Security Questions?
To manage security questions effectively, you should avoid using easily guessable answers and opt for unique, complex responses. Incorporate strong password management practices by storing answers securely and updating them regularly. Use these questions as part of user authentication, but don’t rely solely on them. Instead, combine security questions with multi-factor authentication for enhanced protection, ensuring your account stays secure against unauthorized access.

ANSQUE Security Cameras Wireless Outdoor Home System, 4 Camera Kit, No Subscription Fees, Solar Powered, Local Storage, 365-Day Battery Life, 360°PTZ Surveillance, Auto Tracking, 2K Color Night Vision
No Subscription Fees, Secure Local Storage: AnsqueBase features built-in 32GB local storage with up to 120 days of...
As an affiliate, we earn on qualifying purchases.
Conclusion
Security questions are like broken locks on a fortress—easily picked or guessed, exposing your defenses. They symbolize outdated trust in simple answers over robust protection. As you navigate digital life, remember that relying on these questions leaves your treasures vulnerable, like a house with a flimsy door. To truly safeguard yourself, embrace stronger, modern safeguards—because in the fight against cyber threats, only solid walls can keep your valuables safe from intruders.

ANNKE 3K Lite Wired Security Camera System Outdoor with AI Human/Vehicle Detection, 8CH H.265+ DVR and 8 x 1920TVL 2MP IP67 Home CCTV Cameras with Smart Dual Light, Color Night Vision, 1TB Hard Drive
AI Motion Detection 2.0 – Driving AI to the next level, human&vehicle detection and flexible detection area are...
As an affiliate, we earn on qualifying purchases.

Blink Outdoor 4 – Wireless smart security camera, two-year battery life, 1080p HD day and infrared night live view, two-way talk. Sync Module Core included – 3 camera system
Outdoor 4 is our most affordable wireless smart security camera yet, offering up to two-year battery life for...
As an affiliate, we earn on qualifying purchases.









