To spot fake support scams before calling back, watch out for urgent or threatening messages that pressure you to act quickly. Verify sender email addresses and avoid clicking suspicious links or attachments. Be wary of generic greetings, strange contact details, or requests for remote access and personal info. Fake support sites often look unprofessional with pop-ups or errors. Staying alert and verifying through official sources helps you avoid scams—continue to explore how to stay safe.
Key Takeaways
- Verify the sender’s contact details against official company websites before responding or calling back.
- Look for urgent language or pressure tactics that push for immediate action.
- Check for generic greetings and suspicious email addresses or phone numbers.
- Avoid clicking links or downloading attachments from unknown or unverified sources.
- Confirm support requests through official channels rather than trusting unsolicited messages.
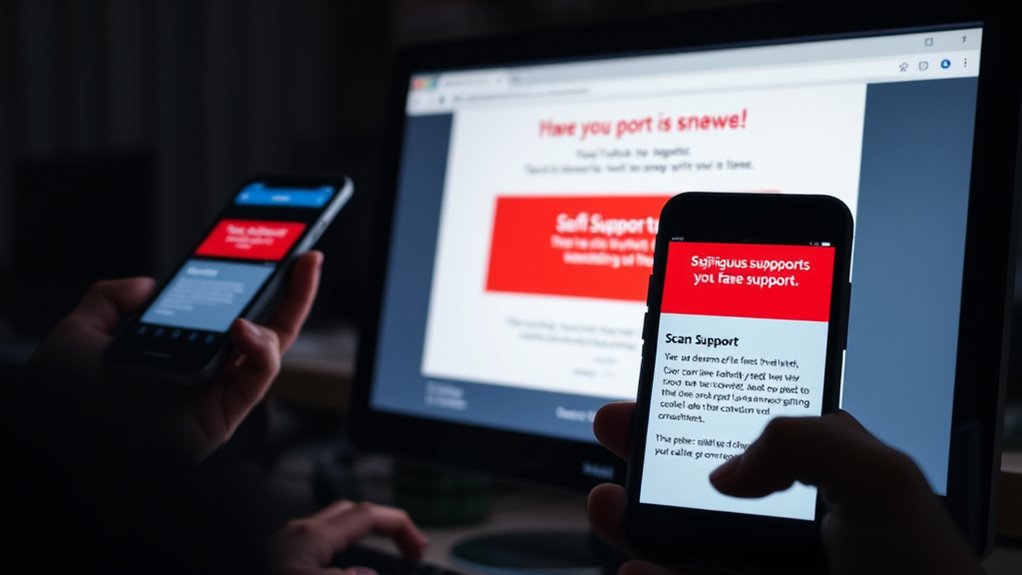
Fake support scams are becoming increasingly common, and it’s essential to know how to recognize them before you fall victim. Scammers often use sophisticated tactics, including phishing techniques, to trick you into revealing personal information or granting remote access to your devices. Being aware of scam warning signs can help you avoid falling for these traps.
One of the most common phishing techniques scammers use involves sending emails or messages that appear to come from legitimate companies or tech support. These messages often create a sense of urgency, claiming there’s a problem with your account or device that needs immediate attention. They might ask you to click on links or download attachments, which can lead to malicious websites designed to steal your information or install malware. Recognizing these scam warning signs early can save you from potential financial loss and identity theft. Always scrutinize the sender’s email address or phone number—scammers often use email addresses that resemble official contacts but contain subtle misspellings or strange domain names. Be wary of generic greetings like “Dear Customer,” instead of addressing you by name, which is a common sign of mass phishing attempts.
Another scam warning sign is if a caller or message pressures you to act immediately, insisting that your device is at risk or your account has been compromised. Legitimate support teams usually don’t operate this way. They won’t rush you into making decisions or demand remote access without proper verification. If someone claims to be from a well-known company but refuses to provide official identification or details, treat it with suspicion. Also, be cautious if they ask for remote access to your computer or to share sensitive information like passwords or credit card numbers. Scammers often pose as support agents to gain control of your device or scam you out of money, so never grant remote access unless you’re absolutely sure of their legitimacy. Additionally, familiarize yourself with support scam tactics to better identify potential threats before they escalate.
Furthermore, be mindful of websites that look suspicious or have a lot of pop-ups and errors. These are often associated with scam sites designed to mimic legitimate support pages. If you’re unsure about a message or call, take a moment to verify the contact through official sources. Use the official website or customer service number, rather than the one provided by the suspicious caller or email. Trust your instincts—if something feels off, it probably is.

aosu Security Cameras Outdoor Wireless, 4 Cam-Kit, No Subscription Required, Solar-Powered, Home Security Cameras System with 360° Pan & Tilt, Auto Tracking, 2K Color Night Vision, Easy Setup
No Subscription Required with aosuBase: All recordings will be encrypted and stored in aosuBase without subscription or hidden...
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
Can Fake Support Scammers Access My Personal Files?
Fake support scammers can’t directly access your personal files unless they trick you into revealing login details or installing malicious software. They often use phishing tactics to lure you into giving up sensitive information, which can lead to data breaches. Stay cautious, never share passwords, and avoid clicking suspicious links. Protect your data by verifying support contacts independently, and remember, legitimate companies won’t pressure you into immediate actions.
Are Fake Support Calls Only Targeting Older Adults?
Are fake support calls only targeting older adults? No, scam prevalence now affects all age groups, though elderly targeting is more common due to their familiarity with technology and higher trust levels. You might think you’re safe, but scammers diversify their tactics. Always stay cautious regardless of your age, keep your personal info secure, and question unfamiliar callers—scams target everyone, not just seniors.
How Can I Verify a Support Representative’s Identity Online?
To verify a support representative’s identity online, start with online authentication by asking for their employee ID or official email address. Check their contact details against the company’s official website. You can also look for a support portal or live chat option to confirm their legitimacy. Never share personal info until you’re confident about their identity, and always initiate contact through official channels.
What Are the Long-Term Risks of Falling for a Fake Scam?
If you fall for a fake support scam, you risk long-term issues like identity theft and financial loss. Scammers can steal your personal information, leading to unauthorized transactions or your identity being used fraudulently. This can cause ongoing stress, damage your credit, and take years to resolve. Protect yourself by verifying support contacts and avoiding sharing sensitive info to prevent these serious consequences.
Do Legitimate Companies Ever Make Unsolicited Support Calls?
Did you know that 56% of people receive a phishing email or fake tech support call annually? Legitimate companies do make unsolicited support calls, but they follow strict protocols and usually verify your identity first. Always be cautious if someone claims to be from tech support unexpectedly. If you’re unsure, hang up and contact the company’s official support number. Never give out personal info during suspicious calls.

Blink Outdoor 4 – Wireless smart security camera, two-year battery life, 1080p HD day and infrared night live view, two-way talk. Sync Module Core included – 3 camera system
Outdoor 4 is our most affordable wireless smart security camera yet, offering up to two-year battery life for...
As an affiliate, we earn on qualifying purchases.
Conclusion
So, next time a “support” call sounds too good to be true, remember, your best move might be to ignore it entirely. Ironically, scammers often make it obvious they’re fake — if you’re paying attention. Trust your instincts, not their pressure tactics. After all, the biggest “help” they offer might just be a scam, waiting to catch you off guard. Stay alert, stay safe, and don’t fall for their tricks — even if they sound convincing.

Blink Outdoor 4 – Wireless smart security camera, two-year battery, 1080p HD day and infrared night live view, two-way talk – 5 camera system
Outdoor 4 is our fourth generation wireless smart security camera that helps you protect your home inside and...
As an affiliate, we earn on qualifying purchases.

Philips Wi-Fi Door Lock, WiFi Smart Lock Keyless Entry Deadbolt for Front Door, Compatible with Alexa & Google Assistant, Remote Control, Built-in WiFi, APP Fingerprint Passcode Unlock, Auto Locking
𝐅𝐥𝐞𝐱𝐢𝐛𝐥𝐞 𝐖𝐚𝐲𝐬 𝐭𝐨 𝐔𝐧𝐥𝐨𝐜𝐤: Unlock the way you want: app, passcode, fingerprint, physical key, or voice via Alexa/Google...
As an affiliate, we earn on qualifying purchases.









