To spot phishing scams in just 10 seconds, focus on quick pattern recognition. Check for generic greetings, misspelled words, and unusual sender addresses. Hover over links to see if URLs match official sites, and be wary of urgent requests for personal info or threatening language. Unexpected attachments or suspicious prompts are red flags. Developing a sharp eye for these signs helps you quickly identify scams—keep going to discover more tips and tricks to stay safe online.
Key Takeaways
- Look for generic greetings and spelling errors indicating unprofessional phishing attempts.
- Hover over links to check for mismatched or suspicious URLs before clicking.
- Notice urgent language or pressure tactics prompting immediate action.
- Be cautious of unexpected attachments or download prompts from unknown sources.
- Examine email headers for inconsistencies to detect spoofed or fake sender information.
Identifying Common Phishing Patterns and Warning Signs
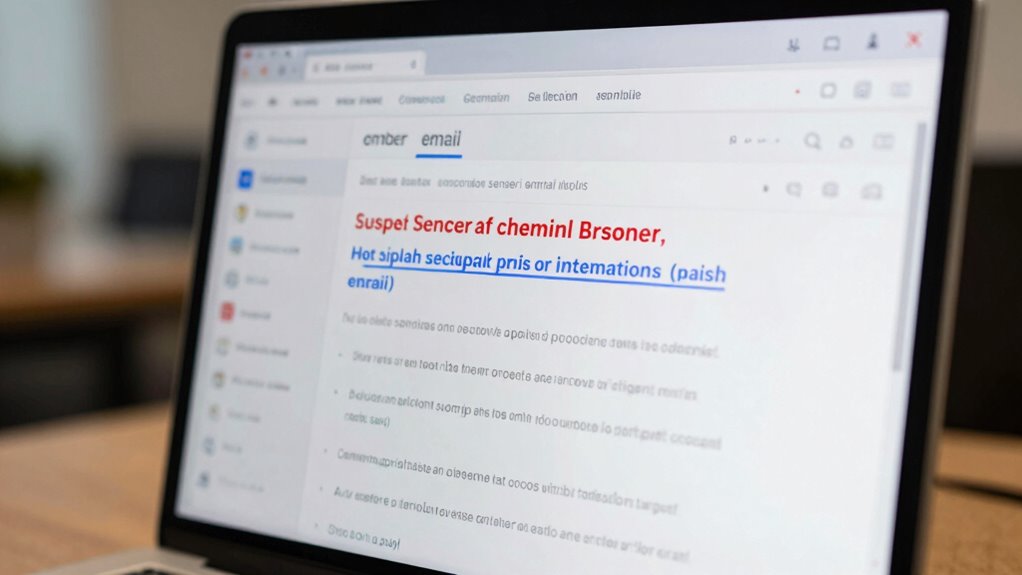
Phishing attacks continue to grow more sophisticated, making it essential for you to recognize common patterns that reveal fraudulent emails. Cybercriminals craft convincing messages that often look legitimate at first glance, but a closer look can expose them. One of the quickest ways to identify a scam is by paying attention to email red flags. These could include generic greetings like “Dear Customer” instead of your name, misspelled words, or unusual sender addresses that don’t match official domains. If an email claims to be from your bank but uses a slightly altered URL or email address, it’s a clear warning sign. Always scrutinize the sender’s email for inconsistencies; scammers often use addresses that resemble legitimate ones but include subtle variations or extra characters. Recognizing the heat distribution and how it influences cooking can help you develop a more cautious approach to digital security, understanding that small anomalies can have significant effects. Being aware of email spoofing techniques can further enhance your ability to spot fake messages. Suspicious links are another red flag that shouldn’t be ignored. Phishers embed malicious URLs within emails that appear trustworthy but redirect you to fake websites designed to steal your login details or install malware. Hover over any link before clicking—if the URL looks strange, mismatched, or unfamiliar, don’t click it. Instead, navigate directly to the company’s official website through your browser to verify if the message is genuine. Many phishing emails also contain urgent language or threats, prompting you to act immediately. Phrases like “Your account will be suspended” or “Verify your information now” are classic tactics to pressure you into making hasty decisions. Another common pattern involves requests for sensitive information. Legitimate organizations rarely ask for passwords, social security numbers, or banking details via email. If you’re asked to provide such data, treat the request skeptically. Always consider whether the message makes sense and whether it’s consistent with past communications from that organization. Be wary of emails that come with unexpected attachments or prompts to download files, as these can contain malware. If an attachment seems suspicious or unfamiliar, don’t open it. Instead, contact the organization directly through official channels to verify the request. Additionally, staying informed about cybersecurity best practices can help you better recognize and respond to these threats. Recognizing common scam patterns and understanding how they exploit human psychology can also make a difference in avoiding falling victim. Paying attention to email header details can reveal discrepancies that are often overlooked by the untrained eye, further aiding in identification.
Frequently Asked Questions
How Can I Verify if an Email Is Genuinely From My Bank?
To verify if an email is genuinely from your bank, start with email verification by checking the sender’s email address carefully—look for subtle misspellings or unusual domains. Always examine bank communication for official branding and contact details. Avoid clicking links or downloading attachments. Instead, contact your bank directly using a verified phone number or their official website. This way, you guarantee the message’s authenticity and protect yourself from scams.
What Are Some Uncommon Signs of Sophisticated Phishing Attempts?
Imagine catching a flicker of movement at the corner of your eye—unusual signs of sophisticated phishing. You notice email forgeries with subtle font mismatches or altered sender details. Suspicious URL patterns, like misspelled domains or extra characters, often hide behind convincing visuals. These signs are harder to spot but essential. Stay alert for emails that seem almost perfect yet reveal tiny inconsistencies, preventing you from falling for advanced scams.
Are There Specific Industries More Targeted by Phishing Schemes?
Certain industries face more targeted attack strategies, making them prime targets for industry-specific scams. For example, finance, healthcare, and tech sectors often encounter sophisticated phishing schemes designed to exploit their unique vulnerabilities. As you handle sensitive data, stay vigilant, recognize industry-specific scam tactics, and implement tailored security measures. Knowing which industries are most targeted helps you better prepare and defend against these targeted attack strategies.
How Frequently Do Phishing Patterns Evolve or Change?
Phishing patterns evolve frequently as cybercriminals adopt evolving tactics to stay ahead. You’ll notice pattern diversity increasing, with attackers constantly changing their methods to bypass security measures. This means you need to stay vigilant, as the tactics aren’t static. Regularly updating your awareness and security tools helps you recognize new phishing schemes, ensuring you don’t fall victim to these ever-changing tactics.
Can AI Detect New Phishing Patterns Effectively?
AI can effectively detect new phishing patterns using advanced pattern recognition and phishing detection algorithms. As you implement these tools, you’ll find they adapt quickly to emerging tactics, identifying subtle changes in phishing schemes. By continuously training AI models on fresh data, you guarantee they stay ahead of evolving threats, making your defenses more robust. This proactive approach helps you catch new phishing attempts before they cause harm.
Conclusion
By recognizing the patterns, spotting the signs, and trusting your instincts, you protect yourself from scams. Stay alert, stay cautious, and stay informed. Every warning sign you notice, every suspicious link you avoid, every time you double-check, you strengthen your defenses. Your vigilance keeps your information safe, your accounts secure, and your peace of mind intact. Remember, in the fight against phishing, your awareness is your greatest weapon—so stay sharp, stay vigilant, and stay safe.