Keeping your remote access secure requires understanding VPNs versus Zero-Trust; discover which approach truly protects your organization.
Browsing Tag
Cybersecurity
13 posts
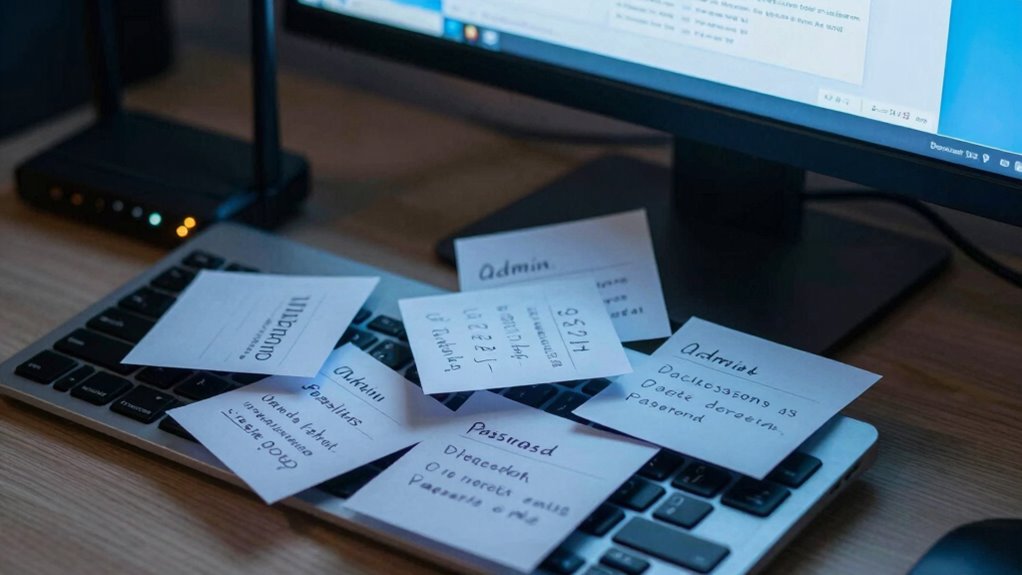
Default Passwords: The Fastest Way Networks Get Compromised
Lurking in default passwords is a major security risk, and understanding how cybercriminals exploit them can help you stay protected.
Secure Deletion: Why “Trash” Isn’t the End
Protect your privacy by understanding why emptying trash isn’t enough and how secure deletion methods can keep your data truly unrecoverable.
How to Spot Fake Support Scams (Before You Call Back)
Concerned about fake support scams? Learn the key signs to identify and avoid these scams before you call back.
Credential Stuffing: Why Reused Passwords Break Everything
Discover how reusing passwords can lead to devastating security breaches and why understanding credential stuffing is crucial for your online safety.
Data Minimization: Reduce Your Attack Surface in 15 Minutes
What if reducing your attack surface took just 15 minutes? Discover how data minimization can protect your system—continue reading to find out how.
Updates and Patches: Why “Later” Is a Real Threat Model
Discover why delaying updates and patches can leave your system vulnerable to threats you can’t afford to ignore.
SIM Swapping: The Account Takeover You Don’t See Coming
Beware of SIM swapping—the covert attack that can hijack your accounts without detection, and learning how to protect yourself is crucial.
Data Leaks: How to Check Exposure Without Panic
Nervous about data leaks? Discover simple steps to check exposure safely and protect your privacy effectively.
Social Engineering: How People Get “Hacked” Without Malware
Never underestimate how social engineering tricks can compromise your security without malware—discover the tactics behind these manipulative strategies.